Some folks in the business are attempting to build a "Security 2.0" paradigm, suggesting that computer security is moving through a second wave of innovation comparable to the developments taking place as part of "Web 2.0".
I disagree that there is a direct correlation between these innovation cycles. Based on our product history, and using the malware vectors and sales channels associated with the different phases of computer usage as reference points, I would argue that we've already experienced two distinct phases of computer security, and are now on the cusp of Security 3.0.
Authentium (then Command Software) shipped its first Security 1.0 product back in 1989 - "Security Guardian" - a system-level PC security product designed to lock down executables.
The focus then was protecting the device against rudimentary forms of malware propagated via what was back then the primary vector - the floppy disk. The distribution channel back then was primarily the retail store or the OEM manufacturer image.
Authentium's second product, F-Prot Pro, back then a co-venture with F-Secure and Frisk Software, shipped in 1992. F-Prot Pro was considered by many to be the first "professional" on-demand antivirus product to enter the market.
Twelve years later, the Authentium ESP suite introduced advanced firewall and URL management functionality and was designed to enable ISPs to provide protection to consumers worried about the "always on" nature of broadband - and the increasing number of attacks targeting the user's personal data, rather than the device.
Interestingly, during this phase, the malware vector and distribution channel became one and the same - the broadband service provider. However, security measures deployed during this phase, including multi-application security suites and two-factor authentication, were largely effective against non-real time criminals and managed to effectively mitigate problems and prevent large-scale financial losses.
The emerging world of Security 3.0 is quite different.
In this world, the PC is no longer the target of attack, nor is the user's generic - and massively cumbersome - accumulated store of personal information.
The criminals invoking Security 3.0 no longer want to sift through your garbage. These criminals understand that the most valuable information obtainable is the information that is most "fresh" - i.e. your stock trading credentials, your two-factor authenticated session keys, the data you are inputting in real-time into your tax form or mortgage application.
Real-time attacks via the Internet may sound like fantasy, but recent attacks on tax filing sites, and online stock trading firms eTrade and TD Waterhouse have shown us it isn't. The evidence isn't only anecdotal: Gartner and other research firms are predicting a renewed focus on access controls, session management, and ID management. There is a ton of venture money pouring into firms, such as Authentium, that offer advanced session-based security solutions.
Time will tell if the investment bring made is large enough. In the world of Security 3.0, criminals are already moving well beyond the dumpsters, focusing their funds on the targeting of users of financial service providers in real time.
They are building advanced systems capable of manipulating hundreds of stolen trading credentials at once - in support of real time buying and selling. They are developing methods of automatically modifying data inputed via forms - again in real-time - using advanced social engineering techniques combined with an array of client and server-side strategies.
One example: earlier in the year, I blogged about a series of "pass-through attacks" involving bogus tax filing sites that popped up a week or two prior to the April 15th tax filing deadline.
These phishing sites were created for one purpose: to replace, in real-time (or in near real-time), the bank account information entered in the "refund" field by the user prior to submission of the tax form to the IRS. The client-side attack took the form of a spoofed email - the server side took the form of a spoofed web site. The targeted information was tax refund and bank account information.
This attack was successful enough to set off alarm bells at the IRS and security companies, globally. However it is nothing compared to what we're going to see happen in the near future.
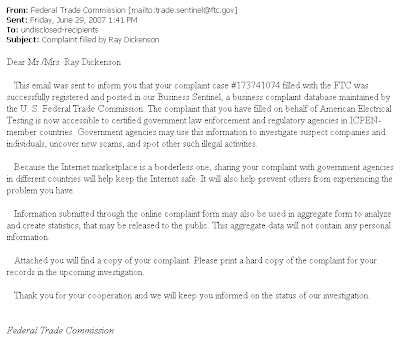
Here's my prediction: Next year, attacks on consumers filing their taxes online will take the form of a targeted "mail-merge" advertising campaign to a subset of high net worth individuals identified using a stolen database (i.e. a replay of the recent BBB and FTC attacks, but with zero spelling mistakes). The attack will involve an email personally addressed to the user. It will be signed by the VP Sales of a leading tax management application manufacturer and carry their brand.
Links in the email will enable host file modifications and lead consumers to a site identical to the manufacturer's site. Once there, consumers will experience services identical to that performed by the manufacturer. They will enter first their names, then their social security numbers, then their addresses, then their personal tax information, then the details of the account they wish their refund to be remitted to.
The attackers will modify their approach during the scam, and consumers will not notice changes in the format of the email or the location of the web sites supporting the scam because their experience will constitute one isolated session. However, during the course of the attack, the criminals will systematically change every aspect of the scam, including hosting companies, receiving bank, and email format. They will also, or course, automate the altering the bank account details of every tax return requiring a refund, as per this year's test run.
The criminal sites will not feel to consumers like fake sites. From a QoS perspective, they will potentially mirror the quality of service of existing sites. Smart criminals will avoid attention by passing through even those tax returns not requiring a refund. The IRS will receive the tax form via the criminal as if it were coming from the consumer (or business) and return to the submitting party an acknowledgment that their form is being processed - via email.
A few months after that, their refund payment will be sent. To a bank far far away. If the criminal gangs involved are clever, millions will be stolen. If they are exceptionally smart, that number could run into the billions within a few short years.
None of are looking forward to this coming true. but come true it will - online criminality is evolving fast and the black hats are as competitive as the rest of us. Unfortunately, two-factor authentication and other systems will not help. As most security professional already know, when it comes to real-time attacks, criminals will profit equally from consumers using 2FA (two factor authentication), as from other simpler forms of authentication.
The good news is that I am increasingly convinced we have an answer to this problem - the results of third party testing and technical evaluations of the past few months have convinced me that we can successfully mitigate many of these issues for consumers.
My objective now is to get this technology to market in large enough numbers to make a difference during the 2008 tax filing season.