Simple Decryption Using Dust Remover
The New York Times reported this week that Princeton University researchers, armed with nothing more than Homeland Security funding and some cans of household dust remover, have come up with a method for cracking even the strongest encryption keys.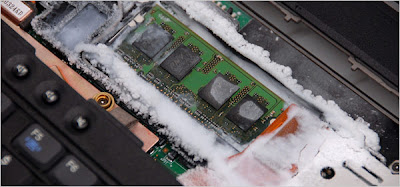
According to the Times' John Markoff:
The move, which cannot be carried out remotely, exploits a little-known vulnerability of the dynamic random access, or DRAM, chip. Those chips temporarily hold data, including the keys to modern data-scrambling algorithms. When the computer’s electrical power is shut off, the data, including the keys, is supposed to disappear.
In a technical paper that was published Thursday on the Web site of Princeton’s Center for Information Technology Policy, the group demonstrated that standard memory chips actually retain their data for seconds or even minutes after power is cut off.
When the chips were chilled using an inexpensive can of air, the data was frozen in place, permitting the researchers to easily read the keys — long strings of ones and zeros — out of the chip’s memory.
In other words, simply by freezing the memory chips on which the keys have been stored, you can cause the data to stay around long enough to decrypt even the longest, most secure keys.
That is not good news for anyone in the defense, media, or communications business.
The usual IT security forums have been abuzz on the topic - and because this hack affects Windows and Linux/Apple OS's equally, the posts have been unusually bipartisan, which makes a nice change.
"Nick", a poster at The Register, articulated the type of hack that is most likely in a corporate or core research environment - a drive-by download based on physical access to a machine that leaves almost no trace:
"The more worrying attack is the 'room temperature' one, where by you could power cycle the machine and dump the memory to the USB drive (as they did), and then leave the scene quickly. The user would just come back and mutter "stupid Windows" at the machine that crashed whilst they were at the coffee machine."
It will be interesting to watch the rebuttals come in over the coming days and weeks - especially those from dedicated security chip manufacturers. Unlike security software development firms like Authentium, hardware security companies typically maintain massive plants and large investments in materials and inventory.
It's anyone's guess as to how these companies will react to this news, and what their researchers will demand in terms of new materials - after all, they are going to need to quickly extend their existing tamper-proofing techniques to include protection against freezing. That won't be cheap , and will probably require new inventories - if in fact it even proves possible.
The first solutions to market will no doubt be neither cheap, fast, or good. But long-term, as long as there are valuable secrets in the world or commercial systems that are dependent on robust keys, there will be *lots* of venture money available for smart folks who think they have the solution to this problem.

